Abstract
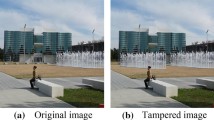
Image forgeries created using easy-to-use image editing tools like Adobe Photoshop have become prime sources of fake news, and are often used in malevolent ways in politics, courtrooms, and in scientific publishing as well. To reduce the problems caused by manipulated images in these domains, it is important to have reliable and fast mechanisms in place for verifying their authenticity before their consumption. Automated detection of image forgeries, is, therefore an ongoing challenge for the research community. One of a commonly used image forgeries is Copy-Move Forgery (CMF), where a region of an image is copied and pasted to some other location within the same image to alter its contents. To detect copy-move forgeries, several Copy Move Forgery Detection (CMFD) techniques have been proposed in the past. However, existing techniques are highly sensitive to post-processing attacks such as noise and compression. In this paper, we propose a new CMFD method in which Cellular Automata (CA) is used for feature extraction. The method works by dividing the input image into overlapping blocks and extracting features from these blocks using the CA inversion procedure. Then, the repeated regions are identified by matching the set of extracted feature vectors. The experimental results show that the detection under noise and compression attacks is accurate compared to many existing methods. As such, the proposed approach may be useful for a variety of CMFD scenarios and may have implications for researchers in related fields.










Similar content being viewed by others
Change history
14 September 2021
A Correction to this paper has been published: https://doi.org/10.1007/s00530-021-00843-0
References
Al-Qershi, O.M., Khoo, B.E.: Evaluation of copy-move forgery detection: datasets and evaluation metrics. Multimed. Tools Appl. 77, 31807–31833 (2018). https://doi.org/10.1007/s11042-018-6201-4
Amerini, I., Ballan, L., Caldelli, R., Bimbo, D.A., Tongo, D.L., Serra, G.: Copy-move forgery detection and localization by means of robust clustering with J-Linkage. Signal Process Image Commun (2013). https://doi.org/10.1016/j.image.2013.03.006.
Roy, A., Konda, A., Chakraborty, R.S.: Copy move forgery detection with similar but genuine objects. In: 2017 IEEE International conference on image processing (ICIP), 2017, pp 4083–4087. https://doi.org/10.1109/ICIP.2017.8297050.
Bik, E.M., Casadevall, A., Fang, F.C.: The prevalence of inappropriate image duplication in biomedical research publications. MBio (2016). https://doi.org/10.1128/mBio.00809-16
Cao, Y., Gao, T., Fan, L., Yang, Q.: A robust detection algorithm for copy-move forgery in digital images. Forensic Sci. Int. 214, 33–43 (2012). https://doi.org/10.1016/j.forsciint.2011.07.015
Christlein, V., Riess, C., Jordan, J., Riess, C., Angelopoulou, E.: An evaluation of popular copy-move forgery detection approaches. IEEE Trans. Inf. Forensics Secur. 7, 1841–1854 (2012). https://doi.org/10.1109/TIFS.2012.2218597
Davarzani, R., Yaghmaie, K., Mozaffari, S., Tapak, M.: Copy-move forgery detection using multiresolution local binary patterns. Forensic Sci. Int. 231, 61–72 (2013). https://doi.org/10.1016/j.forsciint.2013.04.023
Fridrich, J., Soukal, D., Lukáš, J.: Detection of copy-move forgery in digital images. Int. J. Comput. Sci. Issues (2003). https://doi.org/10.1109/PACIIA.2008.240
Gani, G., Qadir, F.: A robust copy-move forgery detection technique based on discrete cosine transform and cellular automata. J. Inf. Secur. Appl. (2020). https://doi.org/10.1016/j.jisa.2020.102510
Hayat, K., Qazi, T.: Forgery detection in digital images via discrete wavelet and discrete cosine transforms. Comput. Electr. Eng. (2017). https://doi.org/10.1016/j.compeleceng.2017.03.013
Huang, Y., Lu, W., Sun, W., Long, D.: Improved DCT-based detection of copy-move forgery in images. Forensic Sci. Int. 206, 178–184 (2011). https://doi.org/10.1016/j.forsciint.2010.08.001
Jeelani, Z., Qadir, F.: Cellular automata-based approach for salt-and-pepper noise filtration. J. King Saud Univ. Comput. Inf. Sci. (2019). https://doi.org/10.1016/j.jksuci.2018.12.006
Jeelani, Z., Qadir, F.: Cellular automata-based approach for digital image scrambling. Int. J. Intell. Comput. Cybern. 11, 353–370 (2018)
Lee, J.C., Chang, C.P., Chen, W.K.: Detection of copy-move image forgery using histogram of orientated gradients. Inf. Sci. (Ny) 321, 250–262 (2015). https://doi.org/10.1016/j.ins.2015.03.009
Li, L., Li, S., Zhu, H., Chu, S.-C., Roddick, J.F., Pan, J.-S.: An efficient scheme for detecting copy-move forged images by local binary patterns. J. Inf. Hiding Multimed. Signal Process. 4, 46 (2013)
Lin, X., Li, J.H., Wang, S.L., Liew, A.W.C., Cheng, F., Huang, X.S.: Recent advances in passive digital image security forensics: a brief review. Engineering (2018). https://doi.org/10.1016/j.eng.2018.02.008
Mahmood, T., Mehmood, Z., Shah, M., Saba, T.: A robust technique for copy-move forgery detection and localization in digital images via stationary wavelet and discrete cosine transform. J. Vis. Commun. Image Represent. 53, 202–214 (2018). https://doi.org/10.1016/j.jvcir.2018.03.015
Mehta, R., Egiazarian, K.: Dominant Rotated Local Binary Patterns (DRLBP) for texture classification. Pattern Recognit. Lett. 71, 16–22 (2016). https://doi.org/10.1016/j.patrec.2015.11.019
Otsu, N.: A threshold selection method from gray-level histograms. IEEE Trans. Syst. Man. Cybern. 9, 62–66 (1979). https://doi.org/10.1109/TSMC.1979.4310076
Qadir, F., Peer, M.A., Khan, K.A.: Digital image scrambling based on two dimensional cellular automata. Int. J. Comput. Netw. Inf. Secur. 5, 36–41 (2013). https://doi.org/10.5815/ijcnis.2013.02.05
Sun, X., Rosin, P.L., Martin, R.R.: Fast rule identification and neighborhood selection for cellular automata. Syst. Man Cybern Part B Cybern, IEEE Trans (2011). https://doi.org/10.1109/TSMCB.2010.2091271
Tralic, D., Zupancic, I., Grgic, S., Grgic, M.: CoMoFoD—New database for copy-move forgery detection. In: Proceedings ELMAR-2013, 2013, pp 49–54.
Tralic, D., Grgic, S., Sun, X., Rosin, P.L.: Combining cellular automata and local binary patterns for copy-move forgery detection. Multimed. Tools Appl. 75, 16881–16903 (2016). https://doi.org/10.1007/s11042-015-2961-2
Wang, H., Wang, H.: Perceptual hashing-based image copy-move forgery detection. Secur. Commun. Netw. 2018, 11 (2018). https://doi.org/10.1155/2018/6853696
Xu, B., Wang, J., Liu, G., Dai, Y.: Image copy-move forgery detection based on SURF. Proc. 2010 2nd Int. Conf. Multimed. Inf. Netw. Secur. MINES 2010, 889–892 (2010). https://doi.org/10.1109/MINES.2010.189
Yan, C., Gong, B., Wei, Y., Gao, Y.: Deep multi-view enhancement hashing for image retrieval. Trans. Pattern Anal. Mach. Intell. (2020). https://doi.org/10.1109/tpami.2020.2975798
Yan, C., Li, Z., Zhang, Y., Liu, Y., Ji, X., Zhang, Y.: Depth image denoising using nuclear norm and learning graph model. ACM Trans Multimed Comput Commun Appl (2021). https://doi.org/10.1145/3404374
Yan, C., Shao, B., Zhao, H., Ning, R., Zhang, Y., Xu, F.: 3D room LAYOUT estimation from a single RGB image. IEEE Trans. Multimed. 22, 3014–3024 (2020)
Zhao, J., Guo, J.: Passive forensics for copy-move image forgery using a method based on DCT and SVD. Forensic Sci. Int. 233, 158–166 (2013). https://doi.org/10.1016/j.forsciint.2013.09.013
Zhao, Y., Billings, S.A.: Neighborhood detection using mutual information for the identification of cellular automata. Syst. Man, Cybern. Part B Cybern, IEEE Trans (2006). https://doi.org/10.1109/TSMCB.2005.859079
Funding
This research did not receive any specific grant from funding agencies in the public, commercial, or not-for-profit sectors.
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
None.
Additional information
Communicated by C. Yan.
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Gani, G., Jeelani, Z. & Qadir, F. Cellular automata-based CMF detection under single and multiple post-processing attacks. Multimedia Systems 28, 257–266 (2022). https://doi.org/10.1007/s00530-021-00828-z
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00530-021-00828-z