Abstract
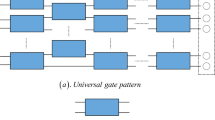
Blind quantum computation (BQC) can ensure a client with limited quantum capability safely delegates computing tasks to a remote quantum server. In order to resist attacks from ignoring identity authentication in BQC protocols, it is necessary to guarantee the legality of both clients and servers in a multi-party BQC network. So we propose a multi-party BQC protocol involving three phases to distribute shared keys and authenticate identities. Firstly, by using the advantages of measurement device independent quantum key distribution (MDI-QKD), the registered client and the assigned server could share the initial key safely in registration phase. Secondly, with the help of semi-honest certificate authority (CA), mutual identity authentication phase realizes the two-way authentication from both sides through the shared key simultaneously. Thirdly, in the blind quantum computing phase, a registered client can complete his computing task by just measuring the qubits from the assigned server rather than preparing the qubits. Moreover, combined with first-in-first-out (FIFO) principle, clients’ authentication and blind quantum computing can be processed in parallel. The protocol can also be applied in other multi-party BQC protocols with the universality of resource states. Compared with other BQC protocols, the reliability of the protocol with identity authentication is guaranteed, and the efficiency will be significantly reflected in real experiments.
Similar content being viewed by others
References
Arrighi P, Salvail L. Blind quantum computation. Int J Quantum Inform, 2006, 4: 883–898
Childs A M. Secure assisted quantum computation. Quantum Inform Comput, 2005, 5: 456–466
Broadbent A, Fitzsimons J, Kashefi E. Universal blind quantum computation. In: Proceedings of 2009 50th Annual IEEE Symposium on Foundations of Computer Science, 2009. 517–526
Li Q, Chan W H, Wu C, et al. Triple-server blind quantum computation using entanglement swapping. Phys Rev A, 2014, 89: 040302
Raussendorf R, Briegel H J. A one-way quantum computer. Phys Rev Lett, 2001, 86: 5188–5191
Greganti C, Roehsner M C, Barz S, et al. Demonstration of measurement-only blind quantum computing. New J Phys, 2016, 18: 013020
Huang H L, Zhao Q, Ma X, et al. Experimental blind quantum computing for a classical client. Phys Rev Lett, 2017, 119: 050503
Huang H L, Bao W S, Li T, et al. Universal blind quantum computation for hybrid system. Quantum Inf Process, 2017, 16: 199
Yin H L, Chen T Y, Yu Z W, et al. Measurement-device-independent quantum key distribution over a 404 km optical fiber. Phys Rev Lett, 2016, 117: 190501
Morimae T, Koshiba T. Impossibility of perfectly-secure delegated quantum computing for classical client. 2014. ArXiv: 1407.1636
Hayashi M, Morimae T. Verifiable measurement-only blind quantum computing with stabilizer testing. Phys Rev Lett, 2015, 115: 220502
Morimae T, Fitzsimons J F. Post hoc verification with a single prover. 2016. ArXiv: 1603.06046
Morimae T. Verification for measurement-only blind quantum computing. Phys Rev A, 2014, 89: 060302
Gheorghiu A, Kashefi E, Wallden P. Robustness and device independence of verifiable blind quantum computing. New J Phys, 2015, 17: 083040
Gheorghiu A, Wallden P, Kashefi E. Rigidity of quantum steering and one-sided device-independent verifiable quantum computation. New J Phys, 2017, 19: 023043
Yang Y G, Wen Q Y. An efficient two-party quantum private comparison protocol with decoy photons and two-photon entanglement. J Phys A-Math Theor, 2009, 42: 055305
Tseng H Y, Lin J, Hwang T. New quantum private comparison protocol using EPR pairs. Quantum Inf Process, 2012, 11: 373–384
Zhang W W, Zhang K J. Cryptanalysis and improvement of the quantum private comparison protocol with semi-honest third party. Quantum Inform Process, 2013, 12: 1981–1990
Wei C Y, Cai X Q, Wang T Y, et al. Error tolerance bound in QKD-based quantum private query. IEEE J Sel Areas Commun, 2020, 38: 517–527
Gao F, Qin S J, Huang W, et al. Quantum private query: a new kind of practical quantum cryptographic protocol. Sci China-Phys Mech Astron, 2019, 62: 70301
Wei C Y, Cai X Q, Liu B, et al. A generic construction of quantum-oblivious-key-transfer-based private query with ideal database security and zero failure. IEEE Trans Comput, 2018, 67: 2–8
Barz S, Kashefi E, Broadbent A, et al. Demonstration of blind quantum computing. Science, 2012, 335: 303–308
Dunjko V, Kashefi E, Leverrier A. Blind quantum computing with weak coherent pulses. Phys Rev Lett, 2012, 108: 200502
Morimae T, Fujii K. Blind quantum computation protocol in which Alice only makes measurements. Phys Rev A, 2013, 87: 050301
Kong X Q, Li Q, Wu C, et al. Multiple-server flexible blind quantum computation in networks. Int J Theor Phys, 2016, 55: 3001–3007
Li Q, Li Z, Chan W H, et al. Blind quantum computation with identity authentication. Phys Lett A, 2018, 382: 938–941
Lo H K, Curty M, Qi B. Measurement-device-independent quantum key distribution. Phys Rev Lett, 2012, 108: 130503
Dunjko V, Fitzsimons J, Portmann C, et al. Composable security of delegated quantum computation. In: Proceedings of the 20th Annual International Conference on the Theory and Application of Cryptology and Information Security, 2014. 406–425
Morimae T, Koshiba T. Composable security of measuring-Alice blind quantum computation. 2013. ArXiv: 1306.2113
Liang M. Blind quantum computation with completely classical client and a trusted center. 2015. ArXiv: 1508.07778
Sheng Y B, Zhou L. Deterministic entanglement distillation for secure double-server blind quantum computation. Sci Rep, 2015, 5: 7815
Briegel H J, Browne D E, Dür W, et al. Measurement-based quantum computation. Nat Phys, 2009, 5: 19–26
Raussendorf R, Browne D E, Briegel H J. Measurement-based quantum computation on cluster states. Phys Rev A, 2003, 68: 022312
Rossi M, Huber M, Bruß D, et al. Quantum hypergraph states. New J Phys, 2013, 15: 113022
Hayashi M, Hajdusek M. Self-guaranteed measurement-based quantum computation. Phys Rev A, 2018, 97: 052308
Childs A M, Leung D W, Nielsen M A. Unified derivations of measurement-based schemes for quantum computation. Phys Rev A, 2005, 71: 032318
Hein M, Dur W, Eisert J, et al. Entanglement in graph states and its applications. 2006. ArXiv: quant-ph/0602096
Zhang X, Luo W, Zeng G, et al. A hybrid universal blind quantum computation. Inf Sci, 2019, 498: 135–143
Gottesman D, Lo H K, Lutkenhaus N, et al. Security of quantum key distribution with imperfect devices. In: Proceedings of International Symposium on Information Theory, 2004. 136
Acknowledgements
This work was supported by National Natural Science Foundation of China (Grant Nos. 61671087, 61962009, 61003287), Huawei Technologies Co. Ltd. (Grant No. YBN2020085019), and the Fund of the Fundamental Research Funds for the Central Universities (Grant No. 2019XD-A02).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Shan, RT., Chen, X. & Yuan, KG. Multi-party blind quantum computation protocol with mutual authentication in network. Sci. China Inf. Sci. 64, 162302 (2021). https://doi.org/10.1007/s11432-020-2977-x
Received:
Revised:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11432-020-2977-x