Abstract
Implementing security and privacy requirements at every level of the software development cycle is imperative for ensuring optimum usability as well as the users’ satisfaction. Software development must consider and comply effectively with the risks involved in the privacy and protection of confidential data. This research study endeavors to integrate the standards of data protection along with the Security Threat Oriented Requirements Engineering (STORE) methodology in order to recognize the potential threats to privacy requirements. The proposed extension of the STORE methodology, called the P-STORE, is validated by a case study of the Healthcare Management Software (HMS) system project. Furthermore, we have used the integrated fuzzy AHP with fuzzy TOPSIS technique for the usability assessment of different privacy requirements engineering approaches including the P-STORE methodology. The study demonstrates that the P-STORE approach has the capability to elicit more efficient privacy requirements and that it allows the software engineer to arrange privacy requirements efficaciously.









Similar content being viewed by others
References
Ari, A.A.A., Ngangmo, O.K., Titouna, C., Thiare, O., Mohamadou, A., & Gueroui, A.M.: Enabling privacy and security in cloud of things: architecture, applications, security & privacy challenges. Appl. Comput. Inf. (2019)
Ansari, M.T.J., & Pandey, D.: Risks, security, and privacy for HIV/AIDS data: Big Data perspective. In: Censorship, Surveillance, and Privacy: Concepts, Methodologies, Tools, and Applications, pp. 58–74. IGI Global (2019)
Zulkernine, M., & Ahamed, S. I.: Software security engineering: toward unifying software engineering and security engineering. In: Enterprise Information Systems Assurance and System Security: Managerial and Technical Issues, pp. 215–233. IGI Global (2006)
Mead, N. R.: Security requirements engineering. Build Security In 2006-08, 10 (2008)
Mai, P.X.; Goknil, A.; Shar, L.K.; Pastore, F.; Briand, L.C.; Shaame, S.: Modeling security and privacy requirements: a use case-driven approach. Inf. Softw. Technol. 100, 165–182 (2018)
Paja, E.; Dalpiaz, F.; Giorgini, P.: Modelling and reasoning about security requirements in socio-technical systems. Data Knowl. Eng. 98, 123–143 (2015)
Baldassarre, M. T., Santa Barletta, V., Caivano, D., & Scalera, M.: Integrating security and privacy in software development. Softw. Qual. J. pp. 1–32 (2020)
Darr, E.: Health Services Management. Health Professions Press, Inc., Baltimore, MD. (1997)
Alotaibi, Y.K.; Federico, F.: The impact of health information technology on patient safety. Saudi Med. J. 38(12), 1173 (2017)
Earp, J.B.; Payton, F.C.: Dirty laundry: privacy issues for IT professionals. IT Prof. 2(2), 51–54 (2000)
Klar, R.: Selected impressions on the beginning of the electronic medical record and patient information. Methods Inf. Med. 43(05), 537–542 (2004)
Roukema, J.; Los, R.K.; Bleeker, S.E.; van Ginneken, A.M.; van der Lei, J.; Moll, H.A.: Paper versus computer: feasibility of an electronic medical record in general pediatrics. Pediatrics 117(1), 15–21 (2006)
Ayatollahi, H.; Bath, P.A.; Goodacre, S.: based versus computer-based records in the emergency department: staff preferences, expectations, and concerns. Health Inf. J. 15(3), 199–211 (2009)
ISO, E.: 27799: 2008 Health informatics. In: Information Security Management in Health Using ISO/IEC, 27002 (2008).
Hash, J.; Bowen, P.; Johnson, A.; Smith, C.D.; Steinberg, D.I.: An introductory resource guide for implementing the health insurance portability and accountability act (HIPAA) security rule. US Department of Commerce, Technology Administration, National Institute of Standards and Technology (2005)
Fassett, W.E.: Patient safety and quality improvement act of 2005. Ann. Pharmacother. 40(5), 917–924 (2006)
David Blumenthal, M.D.: Launching hitech. N. Engl. J. Med. 362(5), 382 (2010)
Austin, L.M.: Reviewing PIPEDA: control, privacy and the limits of fair information practices. Can. Bus. LJ 44, 21 (2006)
Voigt, P., & Von dem Bussche, A.: The EU General Data Protection Regulation (GDPR). A Practical Guide, 1st Ed., Springer International Publishing, Cham (2017)
Taylor, E.: UK schools, CCTV and the Data Protection Act 1998. J. Educ. Policy 26(1), 1–15 (2011)
Rao, S.: Information Technology Act: Consumers' Perspective. Econ. Political Wkly. pp. 3501–3503 (2001)
Team, I. P.: EU General Data Protection Regulation (GDPR): An Implementation and Compliance Guide. IT Governance Ltd (2017)
Tikkinen-Piri, C.; Rohunen, A.; Markkula, J.: EU general data protection regulation: changes and implications for personal data collecting companies. Comput. Law Secur. Rev. 34(1), 134–153 (2018)
Moses, L. B.: Recurring dilemmas: The law's race to keep up with technological change. U. Ill. JL Tech. &Pol'y, 239 (2007)
Danezis, G., Domingo-Ferrer, J., Hansen, M., Hoepman, J. H., Metayer, D. L., Tirtea, R., & Schiffner, S.: Privacy and data protection by design-from policy to engineering. arXiv preprint (2015)
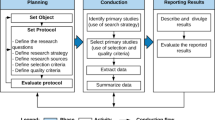
Ansari, M.T.J., Pandey, D., & Alenezi, M.: Store: security threat oriented requirements engineering methodology. J. King Saud Univ. Comput. Inf. Sci. (2018)
Jensen, C.; Tullio, J.; Potts, C.; Mynatt, E.D.: STRAP: A Structured Analysis Framework for Privacy. Georgia Institute of Technology (2005)
Mead, N.R.; Miyazaki, S.; Zhan, J.: Integrating privacy requirements considerations into security requirements engineering method and tool. Int. J. Inf. Priv. Secur. Integr. 1(1), 106–126 (2011)
Deng, M.; Wuyts, K.; Scandariato, R.; Preneel, B.; Joosen, W.: A privacy threat analysis framework: supporting the elicitation and fulfillment of privacy requirements. Requir. Eng. 16(1), 3–32 (2011)
Spiekermann, S.; Cranor, L.F.: Engineering privacy. IEEE Trans. Softw. Eng. 35(1), 67–82 (2008)
Kalloniatis, C.; Kavakli, E.; Gritzalis, S.: Addressing privacy requirements in system design: the PriS method. Requir. Eng. 13(3), 241–255 (2008)
He, Q., & Antón, A. I.: A framework for modeling privacy requirements in role engineering. In: Proceediings of REFSQ, Vol. 3, pp. 137–146 (2003)
Meis, R.: Problem-Based Privacy Analysis (ProPAn): A Computer-aided Privacy Requirements Engineering Method. Universitaet Duisburg-Essen, Germany (2018)
Liu, L., Yu, E., & Mylopoulos, J.: Security and privacy requirements analysis within a social setting. In: Proceedings. 11th IEEE International Requirements Engineering Conference, 2003, pp. 151–161. IEEE (2003)
Beckers, K., Fabender, S., Heisel, M., & Meis, R. A problem-based approach for computer-aided privacy threat identification. In: Annual Privacy Forum, pp. 1–16. Springer, Berlin, Heidelberg (2012)
Dalpiaz, F., Van der Schalk, I., &Lucassen, G.: Pinpointing ambiguity and incompleteness in requirements engineering via information visualization and NLP. In: International Working Conference on Requirements Engineering: Foundation for Software Quality, pp. 119–135. Springer, Cham (2018)
Fernández, D.M.; Wagner, S.: Naming the pain in requirements engineering: A design for a global family of surveys and first results from Germany. Inf. Softw. Technol. 57, 616–643 (2015)
Sharp, H., Finkelstein, A., & Galal, G.: Stakeholder identification in the requirements engineering process. In: Proceedings of Tenth International Workshop on Database and Expert Systems Applications. DEXA 99, pp. 387–391. IEEE (1999)
Fabian, B.; Gürses, S.; Heisel, M.; Santen, T.; Schmidt, H.: A comparison of security requirements engineering methods. Requir. Eng. 15(1), 7–40 (2010)
Glinz, M.; Wieringa, R.J.: Guest editors’ introduction: Stakeholders in requirements engineering. IEEE Softw. 24(2), 18–20 (2007)
Almorsy, M., Grundy, J., & Ibrahim, A. S.: Collaboration-based cloud computing security management framework. In: 2011 IEEE 4th International Conference on Cloud Computing, pp. 364–371. IEEE (2011)
Spiekermann, S.: The challenges of privacy by design. Commun. ACM 55(7), 38–40 (2012)
Mead, N.R.; Stehney, T.: Security quality requirements engineering (SQUARE) methodology. ACM SIGSOFT Softw. Eng. Notes 30(4), 1–7 (2005)
Snyder, W.; Swiderski, F.: Threat modeling. Microsoft Press 35, 36–37 (2004)
Xu, D.; Nygard, K.E.: Threat-driven modeling and verification of secure software using aspect-oriented Petri nets. IEEE Trans. Softw. Eng. 32(4), 265–278 (2006)
Kelly, J.C.; Sherif, J.S.; Hops, J.: An analysis of defect densities found during software inspections. J. Syst. Softw. 17(2), 111–117 (1992)
Porter, A.A.; Votta, L.G.; Basili, V.R.: Comparing detection methods for software requirements inspections: a replicated experiment. IEEE Trans. Softw. Eng. 21(6), 563–575 (1995)
Finkelstein, A., & Fuks, H.: Multiparty specification. In: Proceedings of the 5th International Workshop on Software Specification and Design, pp. 185–195 (1989)
Cysneiros, L. M.: Requirements engineering in the health care domain. In: Proceedings IEEE Joint International Conference on Requirements Engineering, pp. 350–356. IEEE (2002)
Saaty, T.L.: Decision making with the analytic hierarchy process. Int. J. Serv. Sci. 1(1), 83–98 (2008)
Hwang, C. L., & Yoon, K.: Methods for multiple attribute decision making. In: Multiple attribute decision making, pp. 58–191. Springer, Berlin, Heidelberg (1981)
Sharawat, K., & Dubey, S. K.: An approach to vendor selection on usability basis by AHP and fuzzy topsis method. In: Soft Computing: Theories and Applications, pp. 595–604. Springer, Singapore (2018)
Masudin, I., & Saputro, T. E.: Evaluation of B2C website based on the usability factors by using fuzzy AHP & hierarchical fuzzy TOPSIS. In: IOP Conference Series: Materials Science and Engineering, Vol. 114, No. 1, p. 012091. IOP Publishing (2016)
Nagpal, R.; Mehrotra, D.; Bhatia, P.K.; Sharma, A.: Rank university websites using fuzzy AHP and fuzzy TOPSIS approach on usability. Int. J. Inf. Eng. Electron. Bus. 7(1), 29 (2015)
Atalay, K.D.; Eraslan, E.: Multi-criteria usability evaluation of electronic devices in a fuzzy environment. Hum. Factors Ergon. Manuf. Serv. Ind. 24(3), 336–347 (2014)
Cranor, L., & Garfinkel, S.: Security and usability. Retrieved 10 May 2020, from https://www.oreilly.com/library/view/security-and-usability/0596008279/ch04.html
Acknowledgments
This project was supported by Taif University Researchers Supporting Project number (TURSP-2020/107), Taif University, Taif, Saudi Arabia
Funding
Taif University Researchers Supporting Project at Taif University, Taif, Saudi Arabia.
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
Authors have declared that no competing interests exist.
Rights and permissions
About this article
Cite this article
Ansari, M.T.J., Baz, A., Alhakami, H. et al. P-STORE: Extension of STORE Methodology to Elicit Privacy Requirements. Arab J Sci Eng 46, 8287–8310 (2021). https://doi.org/10.1007/s13369-021-05476-z
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s13369-021-05476-z