Abstract
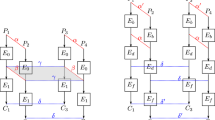
Substitution box is a significant and only nonlinear constituent of block cipher. S-box plays a central role in converting the intelligible message or plain text, into an enciphered format. Construction of strong S-boxes is an important area of interest for security experts. In this work, we develop a new method to evolve S-boxes with the help of coset graph for the action of \(PSL\left( {2,{\mathbb {Z}}} \right)\) on projective line over the finite field GF (28), a special type of bijective map \(g\) and the symmetric group S256 The capability of the proposed S-boxes to mitigate cryptanalysis is investigated through various performance analyzing parameters. The outcomes of the comparison with the familiar S-boxes indicate that the working abilities of newly designed S-boxes are better than that of many of the well-known S-boxes.








Similar content being viewed by others
References
El-Latif, A. A. A., et al. (2020). Providing end-to-end security using quantum walks in IoT networks. IEEE Access, 8, 92687–92696. https://doi.org/10.1109/ACCESS.2020.2992820.
Naif, J. R., Abdul-majeed, G. H., & Farhan, A. K. (2019). Internet of things security using new chaotic system and lightweight AES. Journal of Al-Qadisiyah for Computer Science and Mathematics, 11(2), 45–52.
Shannon, C. E. (1949). Communication theory of secrecy systems. Bell System Technical Journal, 28(4), 656–715.
Daemen, J., & Rijmen, V. (2013). The design of Rijndael: AES-the advanced encryption standard. Berlin: Springer.
Biham, E., & Shamir, A. (1991). Differential cryptanalysis of DES-like cryptosystems. Journal of Cryptology, 4(1), 3–72.
Tran, M. T., Bui, D. K., & Duong, A. D. (2008, December). Gray S-box for advanced encryption standard. In Computational Intelligence and Security, 2008. CIS'08. International Conference on (Vol. 1, pp. 253–258). IEEE.
Hussain, I., Shah, T., & Mahmood, H. (2010). A new algorithm to construct secure keys for AES. International Journal of Contemporary Mathematical Sciences, 5(26), 1263–1270.
Hussain, I., Shah, T., Mahmood, H., Gondal, M. A., & Bhatti, U. Y. (2011). Some analysis of S-box based on residue of prime number. Proc Pak Acad Sci, 48(2), 111–115.
Kim, J., & Phan, R. C. W. (2009). Advanced differential-style cryptanalysis of the NSA's skipjack block cipher. Cryptologia, 33(3), 246–270.
Yi, X., Cheng, S. X., You, X. H., & Lam, K. Y. (1997, November). A method for obtaining cryptographically strong 8*8 S-boxes. In Global Telecommunications Conference, 1997. GLOBECOM'97., IEEE (Vol. 2, pp. 689–693). IEEE.
Hussain, I., Shah, T., Mahmood, H., & Gondal, M. A. (2013). A projective general linear group based algorithm for the construction of substitution box for block ciphers. Neural Computing and Applications, 22(6), 1085–1093.
Wang, Y., Zhang, Z., Zhang, L. Y., Feng, J., Gao, J., & Lei, P. (2020). A genetic algorithm for constructing bijective substitution boxes with high nonlinearity. Information Sciences, 253, 152–166.
Artuğer, F., & Özkaynak, F. (2020). A novel method for performance improvement of chaos-based substitution boxes. Symmetry, 12(4), 571.
Hussain, S., Jamal, S. S., Shah, T., & Hussain, I. (2020). A power associative loop structure for the construction of non-linear components of block cipher. IEEE Access, 8, 123492–123506. https://doi.org/10.1109/ACCESS.2020.3005087.
Ahmad, M., Khaja, I. A., Baz, A., Alhakami, H., & Alhakami, W. (2020). Particle swarm optimization based highly nonlinear substitution-boxes generation for security applications. IEEE Access, 8, 116132–116147. https://doi.org/10.1109/ACCESS.2020.3004449.
Yousaf, M. A., Alolaiyan, H., Ahmad, M., Dilbar, M., & Razaq, A. (2020). Comparison of pre and post-action of a finite abelian group over certain nonlinear schemes. IEEE Access, 8, 39781–39792.
Javeed, A., Shah, T., & Ullah, A. (2020). Construction of non-linear component of block cipher by means of chaotic dynamical system and symmetric group. Wireless Personal Communications, 112, 467–480.
Razaq, A., Alolaiyan, H., Ahmad, M., Yousaf, M. A., Shuaib, U., Aslam, W., et al. (2020). A novel method for generation of strong substitution-boxes based on coset graphs and symmetric groups. IEEE Access, 8, 75473–75490.
ul Islam, F., & Liu, G. (2017). Designing S-box based on 4D-4wing hyperchaotic system. 3D Research, 8(1), 9.
Khan, M. A., Ali, A., Jeoti, V., & Manzoor, S. (2018). A chaos-based substitution box (S-Box) design with improved differential approximation probability (DP). Iranian Journal of Science and Technology, Transactions of Electrical Engineering, 42(2), 219–238.
Ahmad, M., Doja, M. N., & Beg, M. S. (2018). ABC optimization based construction of strong substitution-boxes. Wireless Personal Communications, 101, 1715–1729.
Ahmed, H. A., Zolkipli, M. F., & Ahmad, M. (2019). A novel efficient substitution-box design based on firefly algorithm and discrete chaotic map. Neural Computing and Applications, 31, 7201–7210.
Jamal, S. S., & Shah, T. (2018). A novel algebraic technique for the construction of strong substitution box. Wireless Personal Communications, 99(1), 213–226.
Jamal, S. S., Shah, T., Farwa, S., & Khan, M. U. (2017). A new technique of frequency domain watermarking based on a local ring. Wireless Networks, 25, 1491–1503.
Özkaynak, F., Çelik, V., & Özer, A. B. (2017). A new S-box construction method based on the fractional-order chaotic Chen system. Signal, Image and Video Processing, 11(4), 659–664.
Khan, F. A., Ahmed, J., Khan, J. S., Ahmad, J., & Khan, M. A. (2017, July). A novel substitution box for encryption based on Lorenz equations. In Circuits, System and Simulation (ICCSS), 2017 International Conference on (pp. 32–36). IEEE.
Ullah, A., Jamal, S. S., & Shah, T. (2017). A novel construction of substitution box using a combination of chaotic maps with improved chaotic range. Nonlinear Dynamics, 88(4), 2757–2769.
Ahmad, M., Mittal, N., Garg, P., & Khan, M. M. (2016). Efficient cryptographic substitution box design using travelling salesman problem and chaos. Perspectives in Science, 8, 465–468.
Cameron P. J. (2013). Encyclopaedia of design theory. In Cayley graphs and coset diagrams (pp. 1–9).
Lyndon, R. C., & Paul, E. (2015). Combinatorial group theory (Vol. 89). Berlin: Springer.
Pieprzyk, J., & Finkelstein, G. (1988). Towards effective nonlinear cryptosystem design. IEE Proceedings E-Computers and Digital Techniques, 135(6), 325–335.
Gautam, A., Gaba, G. S., Miglani, R., & Pasricha, R. (2015). Application of chaotic functions for construction of strong substitution boxes. Indian Journal of Science and Technology, 8(28), 1–5.
Alkhaldi, A. H., Hussain, I., & Gondal, M. A. (2015). A novel design for the construction of safe S-boxes based on TDERC sequence. Alexandria Engineering Journal, 54(1), 65–69.
Chen, G., Chen, Y., & Liao, X. (2007). An extended method for obtaining S-boxes based on three-dimensional chaotic Baker maps. Chaos, Solitons & Fractals, 31(3), 571–579.
Tang, G., Liao, X., & Chen, Y. (2005). A novel method for designing S-boxes based on chaotic maps. Chaos, Solitons & Fractals, 23(2), 413–419.
Khan, M., Shah, T., & Gondal, M. A. (2013). An efficient technique for the construction of substitution box with chaotic partial differential equation. Nonlinear Dynamics, 73(3), 1795–1801.
Belazi, A., Khan, M., El-Latif, A. A. A., & Belghith, S. (2017). Efficient cryptosystem approaches: S-boxes and permutation–substitution-based encryption. Nonlinear Dynamics, 87(1), 337–361.
Yi, L., Tong, X., Wang, Z., Zhang, M., Zhu, H., & Liu, J. (2019). A novel block encryption algorithm based on chaotic S-box for wireless sensor network. IEEE Access, 7, 53079–53090. https://doi.org/10.1109/ACCESS.2019.2911395.
Shafique, A. (2020). A new algorithm for the construction of substitution box by using chaotic map. The European Physical Journal Plus, 135(2), 1–13.
Bin Faheem, Z., Ali, A., Khan, M. A., Ul-Haq, M. E., & Ahmad, W. (2020). Highly dispersive substitution box (S-box) design using chaos. ETRI Journal, 42, 619–632.
Gao, W., Idrees, B., Zafar, S., & Rashid, T. (2020). Construction of nonlinear component of block cipher by action of modular group PSL (2,ℤ) on projective line PL(GF(28)). IEEE Access. https://doi.org/10.1109/ACCESS.2020.3010615.
Hussain, I., Shah, T., Gondal, M. A., & Mahmood, H. (2012). Generalized majority logic criterion to analyze the statistical strength of S-boxes. Zeitschrift für Naturforschung A, 67(5), 282–288.
Shifa, A., Afgan, M. S., Asghar, M. N., Fleury, M., Memon, I., Abdullah, S., et al. (2018). Joint Crypto-Stego scheme for enhanced image protection with nearest-centroid clustering. IEEE Access, 6, 16189–16206.
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Razaq, A., Ullah, A., Alolaiyan, H. et al. A Novel Group Theoretic and Graphical Approach for Designing Cryptographically Strong Nonlinear Components of Block Ciphers. Wireless Pers Commun 116, 3165–3190 (2021). https://doi.org/10.1007/s11277-020-07841-x
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11277-020-07841-x