Abstract
Quantum secure direct communication (QSDC) is an important branch of quantum communication that transmits confidential messages directly in a quantum channel without utilizing encryption and decryption. It not only prevents eavesdropping during transmission, but also eliminates the security loophole associated with key storage and management. Recently measurement-device-independent (MDI) QSDC protocols in which the measurement is performed by an untrusted party using imperfect measurement devices have been constructed, and MDI-QSDC eliminates the security loopholes originating from the imperfections in measurement devices so that enable applications of QSDC with current technology. In this paper, we complete the quantitative security analysis of the MDI-QSDC protocols, one based on EPR pairs and one based on single photons. In passing, a security loophole in one of the MDI-QSDC protocols (Niu et al. in Sci Bull 63(20):1345–1350, 2018) is fixed. The security capacity is derived, and its lower bound is given. It is found that the MDI-QSDC secrecy capacity is only slightly lower than that of QSDC utilizing perfect measurement devices. Therefore, QSDC is possible with current measurement devices by sacrificing a small amount in the capacity.


Similar content being viewed by others
References
Bennett, C.H., Brassard, G.: Quantum cryptography: public key distribution and coin tossing. In: Proceedings of the IEEE International Conference on Computers, Systems and Signal Processing, Bangalore, India, pp. 175–179 (1984)
Ekert, A.K.: Quantum cryptography based on Bell’s theorem. Phys. Rev. Lett. 67(6), 661–663 (1991)
Long, G.L., Liu, X.S.: Theoretically efficient high-capacity quantum-key-distribution scheme. Phys. Rev. A 65(3), 032302 (2002)
Bennett, C.H., Brassard, G., Breidbart, S., Wiesner, S.: Quantum cryptography, or unforgeable subway tokens. In: Chaum, D., Rivest, R.L., Sherman, A.T. (eds.) Advances in Cryptology, pp. 267–275. Springer, Boston (1983)
Sun, H., Liu, S., Lin, W., Zhang, K.Y., Lv, W., Huang, X., Huo, F., Yang, H., Jenkins, G., Zhao, Q., Huang, W.: Smart responsive phosphorescent materials for data recording and security protection. Nat. Commun. 5, 3601 (2014)
Deng, F.G., Long, G.L., Liu, X.S.: Two-step quantum direct communication protocol using the Einstein–Podolsky–Rosen pair block. Phys. Rev. A 68(4), 042317 (2003)
Wang, C., Deng, F.G., Long, G.L.: Multi-step quantum secure direct communication using multi-particle Green–Horne–Zeilinger state. Opt. Commun. 253(1–3), 15–20 (2005)
Wang, J., Zhang, Q., Tang, C.J.: Multiparty controlled quantum secure direct communication using Greenberger–Horne–Zeilinger state. Opt. Commun. 266(2), 732–737 (2006)
Wang, C., Deng, F.G., Li, Y.S., Liu, X.S., Long, G.L.: Quantum secure direct communication with high-dimension quantum superdense coding. Phys. Rev. A 71(4), 044305 (2005)
Chen, S.S., Zhou, L., Zhong, W., Sheng, Y.B.: Three-step three-party quantum secure direct communication. Sci. China Phys. Mech. 61(9), 90312 (2018)
Deng, F.G., Long, G.L.: Secure direct communication with a quantum one-time pad. Phys. Rev. A 69(5), 052319 (2004)
Yan, F.L., Zhang, X.Q.: A scheme for secure direct communication using EPR pairs and teleportation. Eur. Phys. J. B 41(1), 75–78 (2004)
Liu, Z.H., Chen, H.W., Liu, W.J.: Information leakage problem in efficient bidirectional quantum secure direct communication with single photons in both polarization and spatial-mode degrees of freedom. Int. J. Theor. Phys. 55(11), 4681–4686 (2016)
Cao, Z.W., Feng, X.Y., Peng, J.Y., Zeng, G.H., Qi, X.F.: Quantum secure direct communication scheme in the non-symmetric channel with high efficiency and security. Int. J. Theor. Phys. 54(6), 1871–1877 (2015)
Wang, S.K., Zha, X.W., Wu, H.: Controlled secure direct communication with seven-qubit entangled states. Int. J. Theor. Phys. 57(1), 48–58 (2018)
Jin, S., Yan-Xiao, G., Ping, X., Shi-Ning, Z., You-Bang, Z.: Quantum secure direct communication by using three-dimensional hyperentanglement. Commun. Theor. Phys. 56(5), 831 (2011)
Xu, G., Xiao, K., Li, Z.P., Niu, X.X., Ryan, M.: Controlled secure direct communication protocol via the three-qubit partially entangled set of states. Comput. Mater. Continua 58(3), 809–827 (2019)
Bebrov, G.: On the generalization and improvement of QSDC efficiency achieved through a quantum channel compression. Quantum Inf. Process. 18(4), 115 (2019)
Wang, M.M., Liu, J.L., Gong, L.M.: Semiquantum secure direct communication with authentication based on single-photons. Int. J. Quantum Inf. 17(03), 1950024 (2019)
Zhukov, A.A., Kiktenko, E.O., Elistratov, A.A., Pogosov, W.V., Lozovik, Y.E.: Quantum communication protocols as a benchmark for programmable quantum computers. Quantum Inf. Process. 18(1), 31 (2018)
Murakami, Y., Nakanishi, M., Yamashita, S., Nakashima, Y., Hagiwara, M.: A Quantum secure direct communication protocol for sending a quantum state and its security analysis. In: Proceedings of the 6th WSEAS International Conference on Information Security and Privacy, pp. 91–97. World Scientific and Engineering Academy and Society (WSEAS), Stevens Point, Wisconsin (2007)
Lu, H., Barbeau, M., Nayak, A.: Keyless semi-quantum point-to-point communication protocol with low resource requirements. Sci. Rep. 9(1), 64 (2019)
Srikara, S., Thapliyal, K., Pathak, A.: Continuous variable direct secure quantum communication using gaussian states. Quantum Inf. Process. 19(4), 1–15 (2020)
Hu, J.Y., Yu, B., Jing, M.Y., Xiao, L.T., Jia, S.T., Qin, G.Q., Long, G.L.: Experimental quantum secure direct communication with single photons. Light Sci. Appl. 5(9), e16144 (2016)
Zhang, W., Ding, D.S., Sheng, Y.B., Zhou, L., Shi, B.S., Guo, G.C.: Quantum secure direct communication with quantum memory. Phys. Rev. Lett. 118(22), 220501 (2017)
Zhu, F., Zhang, W., Sheng, Y., Huang, Y.: Experimental long-distance quantum secure direct communication. Sci. Bull. 62(22), 1519–1524 (2017)
Lum, D.J., Howell, J.C., Allman, M.S., Gerrits, T., Verma, V.B., Nam, S.W., Lupo, C., Lloyd, S.: Quantum enigma machine: experimentally demonstrating quantum data locking. Phys. Rev. A 94(2), 022310–022315 (2016)
Shapiro, J.H., Boroson, D.M., Dixon, P.B., Grein, M.E., Hamilton, S.A.: Quantum low probability of intercept. J. Opt. Soc. Am. B 36(3), B41 (2019)
Del Santo, F., Dakić, B.: Two-way communication with a single quantum particle. Phys. Rev. Lett. 120(6), 060503 (2018)
Massa, F., Moqanaki, A., Baumeler, Ä., Del Santo, F., Kettlewell, J.A., Dakić, B., Walther, P.: Experimental two-way communication with one photon. Adv. Quantum Technol. 2(11), 1900050 (2019)
Qi, R., Sun, Z., Lin, Z., Niu, P., Hao, W., Song, L., Huang, Q., Gao, J., Yin, L., Long, G.L.: Implementation and security analysis of practical quantum secure direct communication. Light Sci. Appl. 8(1), 22 (2019)
CAICT: Research report on the development and application of quantum information technology. Tech. rep. (2019)
Sun, Z., Qi, R., Lin, Z., Yin, L., Long, G., Lu, J.: Design and implementation of a practical quantum secure direct communication system. In: 2018 IEEE Globecom Workshops (GC Wkshps), pp. 1–6. IEEE (2018)
Sun, Z., Song, L., Huang, Q., Yin, L., Long, G.L., Lu, J., Hanzo, L.: Towards practical quantum secure direct communication: a quantum-memory-free protocol and code design. IEEE Trans. Commun. (2020). https://doi.org/10.1109/TCOMM.2020.3006201
Huang, A., Barz, S., Andersson, E., Makarov, V.: Implementation vulnerabilities in general quantum cryptography. New J. Phys. 20(10), 103016 (2018)
Makarov, V., Anisimov, A., Skaar, J.: Effects of detector efficiency mismatch on security of quantum cryptosystems. Phys. Rev. A 74(2), 022313 (2006)
Lydersen, L., Wiechers, C., Wittmann, C., Elser, D., Skaar, J., Makarov, V.: Hacking commercial quantum cryptography systems by tailored bright illumination. Nat. Photonics 4(10), 686–689 (2010)
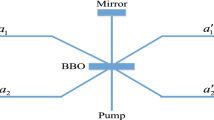
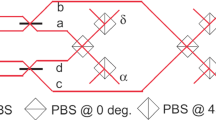
Niu, P.H., Zhou, Z.R., Lin, Z.S., Sheng, Y.B., Yin, L.G., Long, G.L.: Measurement-device-independent quantum communication without encryption. Sci. Bull. 63(20), 1345–1350 (2018)
Zhou, Z., Sheng, Y., Niu, P., Yin, L., Long, G., Hanzo, L.: Measurement-device-independent quantum secure direct communication. Sci. China Phys. Mech. 63(3), 230362 (2020)
Gao, Z., Li, T., Li, Z.: Long-distance measurement-device-independent quantum secure direct communication. EPL 125(4), 40004 (2019)
Zhou, L., Sheng, Y.B., Long, G.L.: Device-independent quantum secure direct communication against collective attacks. Sci. Bull. 65(1), 12–20 (2019)
Kiktenko, E.O., Trushechkin, A.S., Lim, C.C.W., Kurochkin, Y.V., Fedorov, A.K.: Symmetric blind information reconciliation for quantum key distribution. Phys. Rev. Appl. 8(4), 044017 (2017)
Wu, J., Lin, Z., Yin, L., Long, G.L.: Security of quantum secure direct communication based on Wyner’s wiretap channel theory. Quantum Eng. 1(4), e26 (2019)
Lo, H.K., Curty, M., Qi, B.: Measurement-device-independent quantum key distribution. Phys. Rev. Lett. 108(13), 130503 (2012)
Csiszár, I., Korner, J.: Broadcast channels with confidential messages. IEEE Trans. Inform. Theory 24(3), 339–348 (1978)
Renner, R.: Symmetry of large physical systems implies independence of subsystems. Nat. Phys. 3(9), 645–649 (2007)
Kraus, B., Gisin, N., Renner, R.: Lower and upper bounds on the secret-key rate for quantum key distribution protocols using one-way classical communication. Phys. Rev. Lett. 95(8), 080501 (2005)
Holevo, A.S.: Bounds for the quantity of information transmitted by a quantum communication channel. Probl. Peredachi Inf. 9(3), 3–11 (1973)
Das, N., Paul, G.: Improving the security of “ measurement-device-independent quantum communication without encryption”. arXiv preprint arXiv:2006.05263 (2020)
Jozsa, R., Schlienz, J.: Distinguishability of states and von Neumann entropy. Phys. Rev. A 62(1), 012301 (2000)
Acknowledgements
This work was supported by the National Key R&D Program of China (2017YFA0303700), the Key R&D Program of Guangdong province (2018B030325002), the Tsinghua University Initiative Scientific Research Program, the National Natural Science Foundation of China under Grants No. 61727801, No. 11974205, and No. 11774197, and in part by the Beijing Advanced Innovation Center for Future Chip (ICFC).
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Derivation details of secrecy capacity
Derivation details of secrecy capacity
In this appendix, the derivation details of secrecy capacity are presented.
1.1 MDI-TS protocol
For MDI-TS protocol, the derivation focuses on the mutual information between Alice and Eve, i.e., the Holevo bound in Eq. (6) in the main body, which can be simplified through the subadditivity of entropy.
The first term on the right hand side is the von Nuemann entropy of \(\sum _{\zeta } p_{\zeta } \rho _{ABE}^{\zeta } \), which is a result of the cover operation followed with the encoding operation. It is worth noting that the above operations can fully mix the system A and B, respectively, or in other words, they are totally depolarizing channels with the following form,
Take the purified state \(|\varPhi _{ABE}\rangle \) as input, we have
where \(|\varPhi _{ABE}\rangle = \sum _i \sqrt{\delta _i} | \varPsi _i \rangle |E_i \rangle \) and \(\rho _{AB}^{\mathrm {mix}}\) is the fully mixed state of system AB. The result of the partial trace is
Then the first term on the right-hand side of Eq. (6) is
where \(\epsilon _z = \delta _3 + \delta _4\), \(\epsilon _x = \delta _2 +\delta _4\).
Therefore, the mutual information of A and E is
The definition of secrecy capacity leads to Eq. (8) in the main body.
1.2 MDI-DL04 protocol
The derivation for secrecy capacity of MDI-DL04 is similar with Ref. [43]. We also present it here to make this appendix self-contained. For MDI-DL04 protocol, the state \(\rho _{AE}\) has the form
where \(P_{|\cdot \rangle }\) is the projection operator of state \(|\cdot \rangle \) and we have defined:
The encoded states are
Now we consider \(\sigma _u = i \sigma _y\) for brevity, and other situations follow in a similar way. The Holevo bound of AE is
The Gram matrix method [50] is used to calculate the first term, and the Gram matrix of \(\sum _{k} p_k \rho _{AE}^k\) is
Then we have the eigenvalues (noting that \(\delta _1-\delta _2-\delta _3+\delta _4 = 1 - 2\epsilon _y\))
and the entropy \(S\left( \sum _{k} p_k \rho _{AE}^k\right) = 1 + h(\epsilon _y)\). Then we have
and the secrecy capacity in Eq. (10) in the main body follows naturally.
Rights and permissions
About this article
Cite this article
Niu, PH., Wu, JW., Yin, LG. et al. Security analysis of measurement-device-independent quantum secure direct communication. Quantum Inf Process 19, 356 (2020). https://doi.org/10.1007/s11128-020-02840-0
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11128-020-02840-0