Abstract
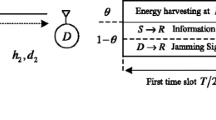
In this paper, we investigate the impact of channel estimation errors on the physical layer security of an overlaying device-to-device (D2D) wireless network with an amplify-and-forward untrusted relay. An untrusted relay assists D2D communication while may capture the confidential data. Under the practical assumption of imperfect channel state information (ICSI) for the relay-to-receiver D2D link, we take into account optimal power allocation (OPA) problem to maximize the achievable secrecy rate of two different scenarios which are without jamming and with friendly jamming. Based on these OPA solutions, we study the secrecy performance of the two scenarios by driving closed-form expressions for the ergodic secrecy rate (ESR) in Rayleigh fading channel. We also calculate the high signal-to-noise ratio (SNR) slope and high SNR power offset of the optimized scenarios by finding the asymptotic ESR. Numerical results confirm the accuracy of our proposed theoretical analysis. The results also demonstrate that our proposed OPAs enhance the ESR performance compared with other power allocation techniques. Moreover, they show the effect of ICSI on the ESR such that as channel estimation error grows, the ESR performance reduction is occurred.







Similar content being viewed by others
References
Rodriguez, L. J., Tran, N. H., Duong, T. Q., Le-Ngoc, T., Elkashlan, M., & Shetty, S. (2015). Physical layer security in wireless cooperative relay networks: State of the art and beyond. IEEE Communications Magazine, 53(12), 32–39.
Kuhestani, A., Mohammadi, A., & Yeoh, P. L. (2018). Security-reliability trade-off in cyber-physical cooperative systems with non-ideal untrusted relaying. In 2018 IEEE 4th world forum on internet of things (WF-IoT) (pp. 552–557). Singapore.
Kuhestani, A., Mohammadi, A., Wong, K., Yeoh, P. L., Moradikia, M., & Khandaker, M. R. A. (2018). Optimal power allocation by imperfect hardware analysis in untrusted relaying networks. IEEE Transactions on Wireless Communications, 17(7), 4302–4314.
Moya Osorio, D. P., Alves, H., & Benitez Olivo, E. E. (2020). On the secrecy performance and power allocation in relaying networks with untrusted relay in the partial secrecy regime. IEEE Transactions on Information Forensics and Security, 15, 2268–2281.
Kuhestani, A., Mohammadi, A., & Yeoh, P. L. (2018). Optimal power allocation and secrecy sum rate in two-way untrusted relaying networks with an external jammer. IEEE Transactions on Communications, 66(6), 2671–2684.
Mamaghani, M. T., Mohammadi, A., Yeoh, P. L., & Kuhestani, A. (2017). Secure two-way communication via a wireless powered untrusted relay and friendly jammer. In 2017 IEEE global communications conference (pp. 1–6). Singapore.
Mabrouk, A., Shafie, A. E., Tourki, K., Al-Dhahir, N., & Hamdi, N. (2020). Securing untrusted full-duplex relay channels in the presence of multiple external cluster-based eavesdroppers. IEEE Systems Journal, 14(1), 665–668.
He, B., Zhou, X., & Abhayapala, T. (2013). Wireless physical layer security with imperfect channel state information: A survey. ZTE Communications, 11(3), 11–19.
Mekkawy, T., Yao, R., Xu, F., & Wang, L. (2017). Optimal power allocation for achievable secrecy rate in an untrusted relay network with bounded channel estimation error. In 26th wireless and optical communication conference (WOCC) (pp. 1–5).
Mekkawy, T., Yao, R., Xu, F., & Wang, L. (2018). Optimal power allocation in an amplify-and-forward untrusted relay network with imperfect channel state information. Wireless Personal Communications, 101(3), 1281–1293.
Zheng, T.-X., & Wang, H.-M. (2016). Optimal power allocation for artificial noise under imperfect CSI against spatially random eavesdroppers. IEEE Transactions on Vehicular Technology, 65(10), 8812–8817.
Yang, T., Zhang, R., Cheng, X., & Yang, L. (2019). Secure massive MIMO under imperfect CSI: Performance analysis and channel prediction. IEEE Transactions on Information Forensics and Security, 14(6), 1610–1623.
Wang, X., Zhang, Z., & Long, K. (2016). Secure beamforming for multiple-antenna amplify-and-forward relay networks. IEEE Transactions on Signal Processing, 64(6), 1477–1492.
Ozduran, V., Yarman, B. S., & Cioffi, J. M. (2016). Impact of channel estimation error on physical layer security in dual-hop half/full-duplex two-way wireless relaying networks. In IEEE conference on computer communications workshops (pp. 308–313).
Lee, K., Lim, J.-T., & Choi, H.-H. (2020). Impact of outdated CSI on the secrecy performance of wireless-powered untrusted relay networks. IEEE Transactions on Information Forensics and Security, 15, 1423–1433.
Asadi, A., Wang, Q., & Mancuso, V. (2014). A survey on device-to-device communication in cellular networks. IEEE Communications Surveys and Tutorials, 16(4), 1801–1819.
Hamoud, O. N., Kenaza, T., & Challal, Y. (2018). Security in device-to-device communications: A survey. IET Networks, 7(1), 14–22.
Wang, L., Shi, Y., Chen, M., Cui, J., & Zheng, B. (2017). Physical layer security in D2D communication system underlying cellular networks. In International conference on wireless communications and signal processing (WCSP) (pp. 1–5).
Mei, W., Chen, Z., & Fang, J. (2017). Outage-constrained secure D2D underlay communication with arbitrarily distributed CSI uncertainty. In IEEE global communications conference (pp. 1–7).
Xu, H., Caire, G., Xu, W., & Chen, M. (2020). Weighted sum secrecy rate maximization for D2D underlaid cellular networks. IEEE Transactions on Communications, 68(1), 349–362.
Zhang, Y., Shen, Y., Jiang, X., & Kasahara, S. (2019). Mode selection and spectrum partition for D2D inband communications: A physical layer security perspective. IEEE Transactions on Communications, 67(1), 623–638.
Ma, B., Zhang, H., & Zhang, Z. (2015). Joint power allocation and mode selection for D2D communications with imperfect CSI. China Communications, 12(7), 73–81.
Huang, S., Mei, W., & Fang, S. (2018). Robust artificial noise-aided transmit optimisation for MISO wiretap channel with device-to-device underlay communication. IET Communications, 12(8), 1019–1027.
Bai, Z., Li, M., Dong, Y., Zhang, H., & Ma, P. (2018). Joint fair resource allocation of D2D communication underlaying downlink cellular system with imperfect CSI. IEEE Access, 6, 63131–63142.
Izanlou, M., Mohammadi, A., & Dosaranian-Moghadam, M. (2019). Optimal power allocation for physical layer security in device-to-device communications using untrusted relays. Transactions on Emerging Telecommunications Technologies. https://doi.org/10.1002/ett.3623.
Gradshteyn, I. S., & Ryzhik, I. M. (2007). Table of integrals, series, and products (7th ed.). New York: Academic.
Tourki, K., & Hasna, M. O. (2016). A collaboration incentive exploiting the primary-secondary systems’ cross interference for PHY security enhancement. IEEE Journal of Selected Topics in Signal Processing, 10(8), 1346–1358.
Lozano, A., Tulino, M., & Verdu, S. (2005). High-SNR power offset in multiantenna communication. IEEE Transactions on Information Theory, 51(12), 4134–4151.
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendices
Appendix 1
Let define \({\upgamma }_{\text{rr}} \triangleq \frac{{{\upgamma }_{{{\text{r}}2}} }}{{{\upgamma }_{{1{\text{r}}}} }}\). Then the pdf of \(\gamma_{rr}\) can be calculated as
where \({{\bar{\upgamma }}}_{rr} \triangleq \frac{{{{\bar{\upgamma }}}_{r2} }}{{{{\bar{\upgamma }}}_{1r} }}\). We remark that \(A_{1}\) is valid since \(\gamma_{1r}\) and \(\gamma_{r2}\) are independent random variables. Moreover, \(A_{2}\) follows from using [26, Eq. 0.410] and \(A_{3}\) follows from substituting the pdfs of \(\gamma_{1r}\) and \(\gamma_{r2}\), and applying [26, Eq. 4.381.4].
Let consider \(\gamma_{rr} + \gamma_{e} = \frac{{\gamma_{r2} }}{{\gamma_{1r} }} + \gamma_{e} = \vartheta\) and \(\gamma_{rr} \le 1.\,{\text{The pdf of }}\vartheta\) is given by
where \(A_{4}\) follows from substituting the cdf of \(\gamma_{e}\) and, \(A_{5}\) follows from replacing the pdf of \(\gamma_{rr} .\) Now, using Eqs. (29) and (31), we have
where using [26, Eq. 3.385], the phrase \(i_{{A_{1} }}\) is obtained as follows
where \(B\left( {x,y} \right)\) is the Beta function [26]
where \({\rm B}\left( {1,1} \right) = 1.\) In Eq. (68), the phrase \(i_{{A_{2} }}\) can be obtained as follows using [26, Eq. 3.382.4]
where \(\varGamma \left( {0, x} \right)\) is in Eq. (34). Therefore, by substituting Eqs. (69) and (71) into Eq. (68), \(I_{{d_{2} }}\) is derived as
Appendix 2
Let define \({\upgamma }_{\text{rr}} \triangleq \frac{{{\upgamma }_{{{\text{r}}2}} }}{{{\upgamma }_{{1{\text{r}}}} }}\), then the pdf of \(\gamma_{rr}\) is as Eq. (66). Under the assumption of \(\gamma_{rr} \le 1,\) the cdf of \(\gamma_{R}\) in Eq. (40) is calculated as
where \(B_{1}\) and \(B_{2}\) follow from substituting the cdf of \(\gamma_{e}\) and the pdf of \(\gamma_{rr} ,\) respectively. Now, using Eq. (31), we get
where
where we applied the change of variable \(u = \gamma^{2} .\) Moreover, regarding [26, Eq. 3.361.1], the phrase \(i_{{B_{1} }}\) is calculated as
and by using the MAPLE, \(i_{{B_{2} }}\) can be expressed as
where \(G_{2 3}^{3 2} \left( {\frac{x + 1}{{{{\bar{\upgamma }}}_{e} }}{|}\begin{array}{*{20}c} {\frac{1}{2},1} \\ {1,1,\frac{1}{2}} \\ \end{array} } \right)\) is expressed as [26, Eq. 9.301]
where the Gamma function \(\varGamma \left( z \right)\) is as follows
As such, \(I_{R}^{\prime}\) can be evaluated as
where
where \(k_{1} = \arctan \left( {\frac{1}{{\sqrt {{{\bar{\upgamma }}}_{rr} - 1} }}} \right)\) and \(k_{2} = {\text{arctan}}\left( {\frac{\sqrt 2 }{{\sqrt {{{\bar{\upgamma }}}_{rr} - 1} }}} \right)\).
Appendix 3
Let define \(A = 1 + \varOmega\) and \(z = \frac{{{\upgamma }_{r2} }}{{{\upgamma }_{1r} }}.\) By applying the change of variable \(U = \sqrt {\frac{A}{1 + z}} ,\) the cdf of \(U\) is given by
where \(F_{Z} \left( z \right)\) was calculated in [25]. Using Eq. (31), \(I_{R}^{\prime L}\) is obtained as
where the integral expressions \(i_{{C_{1} }}\) and \(i_{{C_{2} }}\) can be obtained by using the MAPLE software, as follows
Therefore, by substituting Eqs. (84) and (85) into Eq. (83), \(I_{R}^{\prime L}\) is obtained as follows
Rights and permissions
About this article
Cite this article
Izanlou, M., Mohammadi, A. & Dosaranian-Moghadam, M. Impact of Imperfect Channel State Information on the Physical Layer Security in D2D Wireless Networks Using Untrusted Relays. Wireless Pers Commun 116, 341–368 (2021). https://doi.org/10.1007/s11277-020-07718-z
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11277-020-07718-z