Abstract
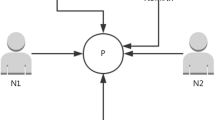
A three-party quantum key injection scheme based on quantum entanglement correlation and local operation of W states is proposed, and a detailed security analysis is provided. As a complete method of entanglement channel key injection, this scheme encodes the key information in W state, which travels more stably in a quantum channel. The measurement result can be modified with a correction scheme or the Mod-2 operation after measuring the particles in quantum registers with Z basis, so that the two receivers will obtain the same key. This scheme is based on the entanglement correlation of the state to carry out the security detection of the key, so the key injector cannot obtain any information about the key, which is of great significance in the field of key management.


Similar content being viewed by others
References
Bennett, C.H., Brassard, G.: Quantum cryptography: public key distribution and coin tossing. In: Proceedings of IEEE International Conference on Computers, Systems, and Signal Processing Bangalore, India, pp 175–179 (1984)
García-Patrón, R., Cerf, N.J.: Continuous-variable quantum key distribution protocols over noisy channels [J]. Phys. Rev. Lett. 102(13), 130501 (2009)
Sasaki, T., Yamamoto, Y., Koashi, M.: Practical quantum key distribution protocol without monitoring signal disturbance [J]. Nature 509(7501), 475 (2014)
Soh, D.B., Brif, C., Coles, P.J., Lütkenhaus, N., Camacho, R.M., Urayama, J., Sarovar, M.: Self-referenced continuous-variable quantum key distribution protocol [J]. Phys. Rev. X 5(4), 041010 (2015)
Peter, S., Stefan, R., Martin, S.: Quantum key management, applied cryptography and network security, Dr. Jaydip Sen (Ed.), ISBN: 978-953-51-0218-2, InTech
Xu, G., Chen, X.B., Dou, Z., et al.: A novel protocol for multiparty quantum key management [J]. Quantum Inf. Process 14(8), 2959–2980 (2015)
Xiao, Y., Rayi, V.K., Sun, B., et al.: A survey of key management schemes in wireless sensor networks [J]. Comput. Commun. 30(11-12), 2314–2341 (2007)
Fumy, W., Landrock, P.: Principles of key managment [J]. IEEE Journal on Selected Areas in Communications 5(11), 785–793 (1993)
Gisin, N., Grégoire, R., Tittel, W., et al.: Quantum cryptography [J]. Review of Modern Physics 74(1), 145–195 (2002)
Toyran, M.: Quantum cryptography [C]. Signal Processing and Communications Applications, 2007. SIU 2007. IEEE 15th IEEE (2007)
Dusek, M., Lutkenhaus, N., Hendrych, M.: Quantum cryptography [J]. Physics, pp. 239–249 (2006)
Boyer, M., Kenigsberg, D., Mor, T.: Quantum key distribution with classical Bob. Phys. Rev. Lett. 99(14), 140501 (2007)
Zhu, K.N., Zhou, N.R., Wang, Y.Q., Wen, X.J.: Semi-quantum key distribution protocols with GHZ states [J]. Int. J. Theor. Phys. 57(12), 3621–3631 (2018)
Zhou, N.R., Zhu, K.N., Zou X. F.: Multi-party semi-quantum key distribution protocol with four-particle cluster state [J]. Annalen Der Physik 531(8), 1800520 (2019)
Krawec, W.O.: Mediated semi-quantum key distribution. Phys. Rev. A 91(3), 032323 (2014)
Chen, Y.B., Chen, H.L., Gong, L.H.: Quantum key injection scheme [J]. Journal of Nanchang University (Natural Science) 37(6), 581–584 (2016)
Dür, W., Vidal, G., Cirac, J.I.: Three qubits can be entangled in two inequivalent ways [J]. Phys. Rev. A 62(6), 062314 (2000)
Zhuan Sun, S.S., Chen, H., Cai, X.X.: QDKD Based on W state and Bell state entanglement [J]. Chinese Journal of quantum electronics 32(2), 178–185 (2015)
Cabello, A.: Quantum key distribution in the Holevo limit [J]. Phys. Rev. Lett. 85(26), 5635–5638 (2000)
Acknowledgments
This work is supported by the National Natural Science Foundation of China (Grant No. 61871205 and 61561033).
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Chen, M., Wang, B., Chen, HY. et al. Three-Party Quantum Key Injection Scheme with W States. Int J Theor Phys 59, 2008–2015 (2020). https://doi.org/10.1007/s10773-020-04472-7
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10773-020-04472-7