Abstract
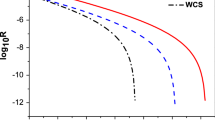
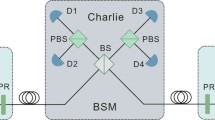
The performance of measurement-device-independent quantum key distribution (MDI-QKD) with three-intensity decoy-state is completely analyzed. The statistical fluctuation based on the central limit theorem is also considered both in symmetric and asymmetric cases. Our simulation results show that in the MDI-QKD system, the choice of the decoy state intensities is more important than the choice of the signal state. More significantly, the ratio between Alice’s signal state optimal intensities and decoy state is well approximately equal to Bob’s in the asymmetric case. These results can be used to optimize the practical quantum communication system.






Similar content being viewed by others
References
Bennett, C.H., Brassard, G.: Quantum cryptography: public key distribution and coin tossing. Proc. IEEE Int. Conf. Comput. Syst. Signal Process. 560, 7 (2014)
Ekert, A.K.: Quantum cryptography based on Bell’s Theorem. Phys. Rev. Lett. 67, 661 (1991)
Gisin, N., Ribordy, G., Tittel, W., Zbinden, H.: Quantum cryptography. Rev. Mod. Phys. 74, 145 (2002)
Huttner, B., Imoto, N., Gisin, N., Mor, T.: Quantum cryptography with coherent states. Phys. Rev. A 51, 1863 (1995)
Scarani, V., Bechmann-Pasquinucci, H., Cerf, N.J., et al.: The security of practical quantum key distribution. Rev. Mod. Phys. 81, 1301 (2009)
Lo, H.-K., Curty, M., Tamaki, K.: Secure quantum key distribution. Nat. Photon. 8, 595 (2014)
Diamanti, E., Lo, H.-K., Yuan, Z.: Practical challenges in quantum key distribution. NPJ Quantum Inf. 2, 16025 (2016)
Brassard, L., Mor, Sanders: Limitations on Practical Quantum Cryptography. Phys. Rev. Lett. 85, 6 (2000)
Lydersen, L., Wiechers, C., Wittmann, C., et al.: Hacking commercial quantum cryptography systems by tailored bright illumination. Nat. Photon. 4, 686 (2010)
Hwang, W.-Y.: Quantum key distribution with high loss: toward global secure communication. Phys. Rev. Lett. 91, 5 (2003)
Lo, H.-K., Ma, X., Chen, K.: Decoy state quantum key distribution. Phys. Rev. Lett. 94, 230504 (2005)
Wang, X.-B.: Beating the photon-number-splitting attack in practical quantum cryptography. Phys. Rev. Lett. 94, 230503 (2005)
Lo, H.-K., Curty, M., Qi, B.: Measurement-device-independent quantum key distribution. Phys. Rev. Lett. 108, 130503 (2012)
Zhou, Y.-H., Yu, Z.-W., Wang, X.-B.: Making the decoy-state measurement-device-independent quantum key distribution practically useful. Phys. Rev. A 93, 042324 (2016)
Wang, Q., Zhou, X.-Y., Guo, G.-C.: Realizing the measure-device-independent quantum-key-distribution with passive heralded-single photon sources. Sci. Rep. 6, 35394 (2016)
Jiang, C., Yu, Z.-W., Wang, X.-B.: Measurement-device-independent quantum key distribution with source state errors in photon number space. Phys. Rev. A 94, 062323 (2016)
Comandar, L.C., Lucamarini, M., Fröhlich, B., et al.: Quantum key distribution without detector vulnerabilities using optically seeded lasers. Nat. Photon. 10, 312 (2016)
Yin, H.-L., Chen, T.-Y., Yu, Z.-W., et al.: Measurement-device-independent quantum key distribution over a 404 km optical fiber. Phys. Rev. Lett. 117, 190501 (2016)
Wang, C., Yin, Z.-Q., Wang, S., et al.: Measurement-device-independent quantum key distribution robust against environmental disturbances. Optica 4, 1016 (2017)
Wang, X.-B.: Three-intensity decoy-state method for device-independent quantum key distribution with basis-dependent errors. Phys. Rev. A 87, 012320 (2013)
Lo, H.-K., Chau, H.F., Ardehali, M.: Efficient quantum key distribution scheme and a proof of its unconditional security. J. Cryptol. 18, 133 (2005)
Xu, F., Curty, M., Qi, B., Lo, H.-K.: Practical aspects of measurement-device-independent quantum key distribution. New J. Phys. 15, 113007 (2013)
Ma, X., Fung, C.-H.F., Razavi, M.: Statistical fluctuation analysis for measurement-device-independent quantum key distribution. Phys. Rev. A 86, 052305 (2012)
Yu, Z.-W., Zhou, Y.-H., Wang, X.-B.: Statistical fluctuation analysis for measurement-device-independent quantum key distribution with three-intensity decoy-state method. Phys. Rev. A 91, 032318 (2015)
Mao, C.-C., Zhou, X.-Y., Zhou, J.-R., et al.: Improved statistical fluctuation analysis for measurement-device-independent quantum key distribution with four-intensity decoy-state method. Opt. Express 26, 13289 (2018)
Jiang, C., Yu, Z.-W., Wang, X.-B.: Measurement-device-independent quantum key distribution with source state errors and statistical fluctuation. Phys. Rev. A 95, 032325 (2017)
Trushechkin, A.S., Kiktenko, E.O., Fedorov, A.K.: Practical issues in decoy-state quantum key distribution based on the central limit theorem. Phys. Rev. A 96, 022316 (2017)
Xu, F., Xu, H., Lo, H.-K.: Protocol choice and parameter optimization in decoy-state measurement-device-independent quantum key distribution. Phys. Rev. A 89, 052333 (2014)
Rubenok, A., Slater, J.A., Chan, P., et al.: Real-World Two-Photon Interference and Proof-of-Principle Quantum Key Distribution Immune to Detector Attacks. Phys. Rev. Lett. 111, 130501 (2013)
Hu, X.-L., Cao, Y., Yu, Z.-W., Wang, X.-B.: Measurement-device-independent quantum key distribution over asymmetric channel and unstable channel. Sci. Rep. 8, 17634 (2018)
Acknowledgements
This work is supported by National Natural Science Foundation of China (Grant No. 61571060), Ministry of Science and Technology of China (Grant No. 2016YFA0301300) and Fundamental Research Funds for the Central Universities (Grant No. 2019XD-A02).
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Liang, W., Xue, Q. & Jiao, R. The performance of three-intensity decoy-state measurement-device-independent quantum key distribution. Quantum Inf Process 19, 165 (2020). https://doi.org/10.1007/s11128-020-02666-w
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11128-020-02666-w